Which Wireless Security Standards Uses a 128-bit Key
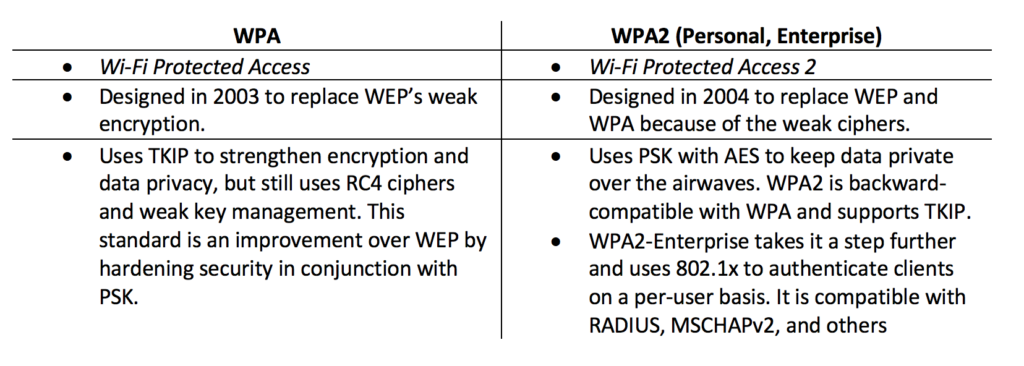
Descriptive that solves the susceptibility to related-key. This is used by WPA.

2020 Nueva Xiaomi Mijia Ai Camara Ip Inteligente 1080p Ip65 Impermeable Full Hd Calidad Infrarroja Vision Nocturna 170 Grados Super Gran Angular Camara Ip Gran Angular Monturas De Gafas Para Hombre
Indicating that the Length field is 2 octets.

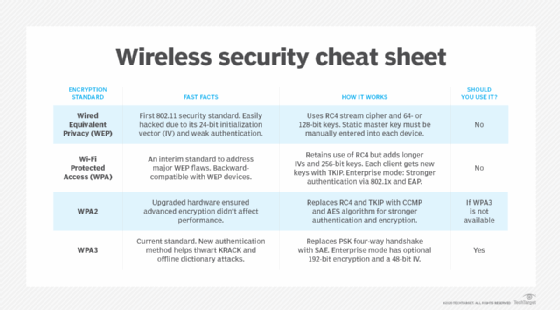
. Indicating that the MIC is 8 octets eight bytes. RC4 TKIP and AES all employ wireless keys of varying lengths. Cybersecurity experts detect many vulnerabilities of this first Wireless Security Protocol.
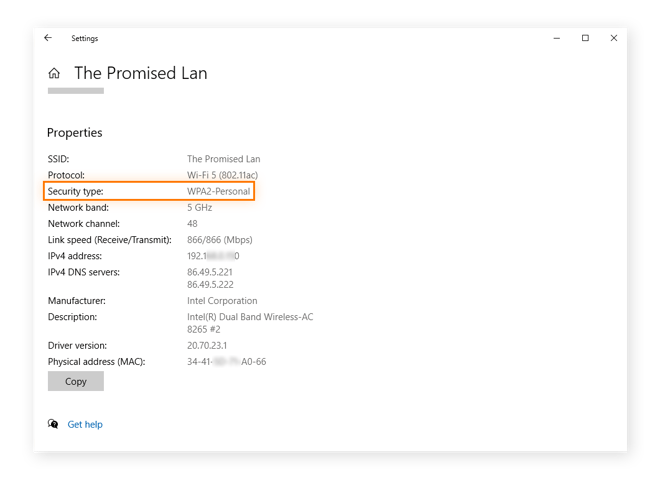
The original and flawed wireless security protocol is known as _____. WEP could use a 64-bit or 128-bit security key but it was a static key. The first is the MAC header which contains the.
Which of the following wireless IEEE standards operate on the 24 GHz radio frequency and are directly compatible with each other. Which field describes the version of 80211 that is being used. For the past many years the standard of the 80211 have changed so much.
WPA-PSK WPA Pre - Shared Key It was developed for use in home and small offices and does not need any authentication server. WPA3-Personal uses CCMP-128 and AES-128. WPA2 introduced Advanced Encryption Standard as a replacement for TKIP.
WPA3-Enterprise has optional 192-bit security encryption and a 48-bit IV for heightened protection of sensitive corporate financial and governmental data. CCMP CTR mode with CBC-MAC Protocol. It requires a complicated setup and provides automatic key generation and additional security measures.
WEP was widely used but it has too vulnerable to the password hacks. Remember that higher the length of the key the better your message is protected. The former uses a 64-bit key whereas the latter uses a 128-bit key.
These wireless keys are hexadecimal numbers that vary in lengthtypically between 128 and 256 bits longdepending on the encryption method used. There are WEP WPA WPA2 and WPA3 wireless security protocols. FTTP is a technology that uses fiber to bring an internet connection to a building or home.
WEP Wired Equivalent Privacy was approved as a Wi-Fi security standard in September 1999. CCMPAES uses several enhancementsincluding temporal keys TKpacket numbers PNnonce number or bit string used only onceupper layer encryptionand additional authentication data AAD. Secure Device Management KTS Wireless provides its customers with management tools used to configure devices and networks.
After the restrictions 128-bit and 256-bit WEP has developed. Of those two options WEP is 128 is more secure. WEP is not very secure and has been mostly phased out.
The original flawed wireless security protocol is known as. Fiber To The Premises. Wi-Fi Protected Access WPA Another common and widely used.
The strength of the key depends on its length. A CCMP Medium Access Control Protocol Data Unit MPDU comprises five sections. The keys used by WPA are 256-bit a significant increase over the 64-bit and 128-bit keys used in the WEP system.
Security Knowledge Security Encyclopedia Security Forum. The higher the length the better. Initially WEP was expected to offer the same security level for wireless networks as wired networks do however there are a lot of well-known issues in WEP which are easy to exploit.
The RC4 stream cipher is used with a 128-bit per-packet key meaning that it dynamically generates a new key for each packet. So WEP was using 64-bit encryption. AES uses a 128-bit key and encrypts data in 128-bit blocks.
This is used by WPA. An 80211 frame contains a number of fields. PKI is recommended as mentioned earlier.
An Overview of Wireless Networking Standards and encryption standards. At the beginning maximum 64-bit encryption was allowed in US. CCMP uses CCM with the following two parameters.
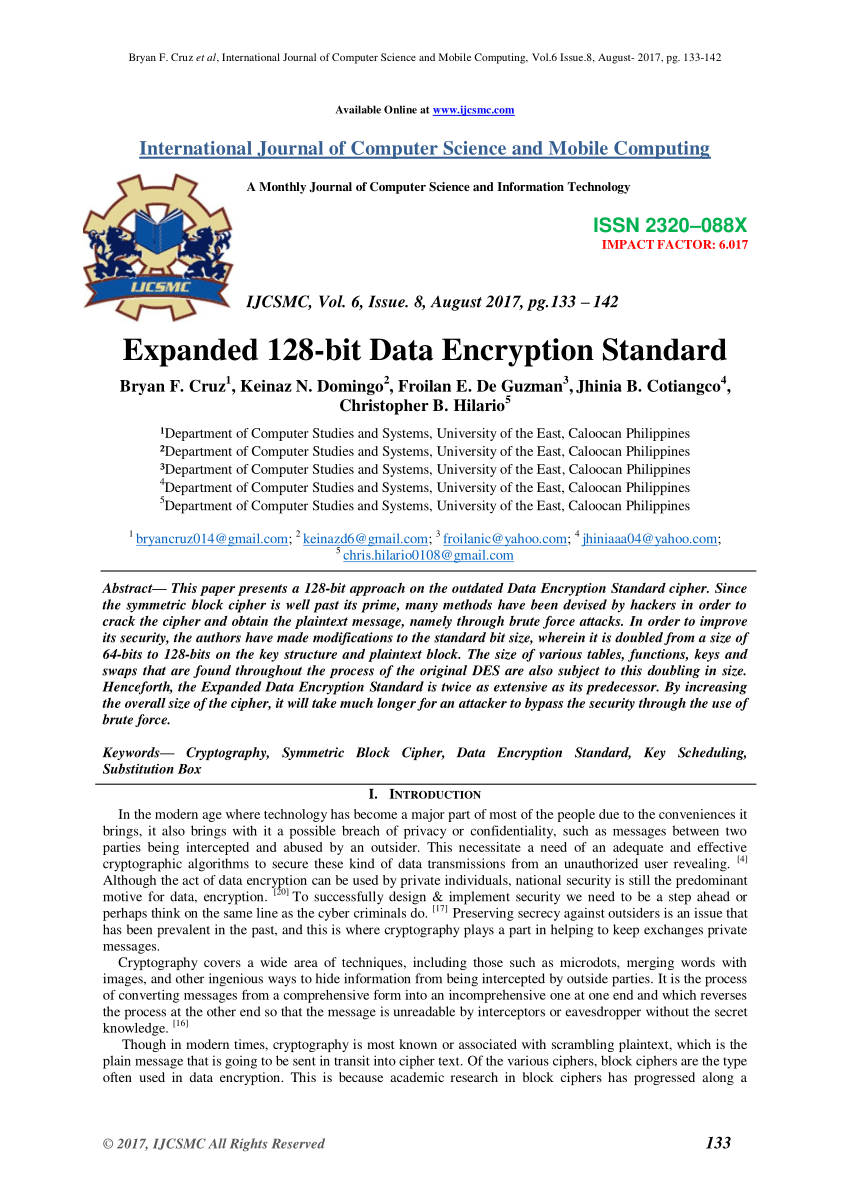
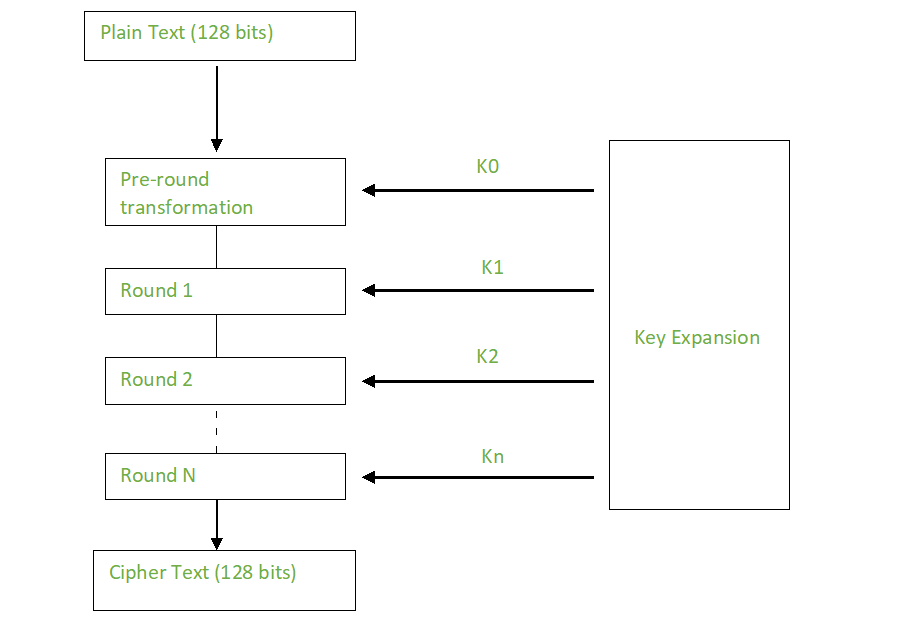
The AES algorithm has several key models such as 128 192 and 256 bits to encrypt and decrypt data on 128-bit message blocks. WPA stands for _______. AES uses a 128-bit key and encrypts data in 128-bit blocks.
AES and CCMP came after TKIP. WPA3 Enterprise is for enterprise uses primarily enforces minimum 128-bit authentication encryption 256-bit key derivation encryption and the use of an authentication server instead of a password. Unfortunately however both WEP 64 nor WEP 128 are vulnerable to various exploits so its recommended that you use a different security standard for your small businesss Wi-Fi.
TKIP introduced a dynamic per-packet key. It uses various Extensible Authentication Protocol EAP for authenticating various categories of network users. As the limitation was withdrawn the 128 bit and 256 bit WEP encryption were developed and came into the wireless security market though 128 became standard.
Which type provide speeds above 1544 megabits per second. The wireless networking is done in the same manner all over the world. Which wireless security standards uses a 128 bit key.
This study uses a 128-bit key. Wi-Fi Protected Access WPA Wi-Fi Protected Access WPA was the next Wi-Fi Alliances project that replaced the WEP standards increasingly noticeable vulnerabilities. KTS Wireless devices use NIST standard AES-128-CCM encryption for the wireless link.
In other words your key length can be anything between 128 0s to 128 1s. So there is the standard which has been fixed by the relevant authorities so that everyone can follow the same standard. It also standardizes the 128-bit cryptographic suite and disallows obsolete security protocols.
WPA is an update to WEP thats much more secure. CCMP is based on AES processing and uses a 128-bit key and a 128-bit block size. Some of the significant changes implemented with WPA included message integrity checks to determine if an attacker had captured or altered packets passed between the access point and client and the Temporal Key Integrity Protocol TKIP.
Ratified in a 2004 IEEE standard Temporal Key Integrity Protocol TKIP uses a dynamically-generated per-packet key. The 128-bit key is provided either by Pre-Shared Key PSK or through the PKI system. Which wireless security standards uses a 128-bit key.
Each packet sent has a unique temporal 128-bit key See. The encryption method is commonly referred to as CCMPAES. Keys with longer length 128 bit or above are almost unbreakable since it takes several to couple of hundred years to break them with the modern.
CCMPAES uses several enhancements including temporal keys TK packet numbers PN nonce number or bit string used only once upper layer encryption and additional authentication data AAD.

Xiaomi R03 Wifi Amplifier Pro Black In 2021 Digital Antenna Xiaomi Wifi

Tp Link Tl Wn725n Nano Adaptateur Usb Sans Fil Wifi N 150 Mbps Amazon Fr Informatique Usb Adapter 150mbps Tp Link

Wep Vs Wpa Vs Wpa2 Vs Wpa3 Fs Community

Logitech M165 Wireless Mouse Plug And Play This Mouse Is Easy To Use As A Mouse With A Cord Just Plug The Receiver Int Logitech Wireless Mouse Logitech Mouse

Comptia A Certification Washington Dc Asm Rockville Maryland Asm Rockville Maryland Comptia A Computer Learning Information Technology
Wi Fi Security Wep Vs Wpa Or Wpa2 Avast
Understanding Wi Fi Authentication A Refresher Aruba Blogs

Edup High Speed 11ac 1300m 2 4g 5 8g Dual Band Wifi Usb3 0 Adapter Dongle 5dbi Antenna Support Desktop Windows Mac Os Ep Ac1686 In 2022 Dual Band Antenna Mac Os
Pdf Expanded 128 Bit Data Encryption Standard

Wifi Encryption Demystified Bmp 1200 927 Cybersecurity Infographic Computer Network Computer Programming

The Difference Between Wep Wpa And Wpa2 Msinfokom

Wpa Key Wpa2 Wpa3 And Wep Key Wi Fi Security Explained

Lenovo Thinkpad X1 Carbon 5 Business Ultrabook Lenovo Thinkpad Lenovo Laptop Design
What Is Counter Mode With Cipher Block Chaining Message Authentication Code Protocol Ccmp
Advanced Encryption Standard Aes Geeksforgeeks

Wi Fi Security Evolution How We Ended Up In Wpa3

Linksys Official Support Setting Up 64 Bit Wep Wireless Security On An Access Point


Comments
Post a Comment